Cyber Security Challenge UK
How I won the first cipher challenge
As announced on https://cybersecuritychallenge.org.uk, I was very excited to learn that I was the first person in the whole country to correctly solve the Cyber Security Challenge UK cipher challenge. Rather appropriately, the mystery prize turned out to be a season ticket for the Bletchley Park site, along with a special guided visit to the National Museum of Computing, including the famous World War II code breaking computer Colossus.
They've published a methodology for solving the challenge, but here's how I did it...
The challenge was to find a hidden code in the cipher message presented on their website. This sounded fun, so I thought I'd give it a quick look:
/9j/4AAQSkZJRgABAQEAYABgAAD/4QBaRXhpZgAATU0AKgAAAAgABQMBAAUAAAABAAAASgMDAAEA AAABAAAAAFEQAAEAAAABAQAAAFERAAQAAAABAAAOxFESAAQAAAABAAAOxAAAAAAAAYagAACxj//b AEMACAYGBwYFCAcHBwkJCAoMFA0MCwsMGRITDxQdGh8eHRocHCAkLicgIiwjHBwoNyksMDE0NDQf Jzk9ODI8LjM0Mv/bAEMBCQkJDAsMGA0NGDIhHCEyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIy etc...
Initial thoughts
I only wanted to spend a few minutes on this, but the initial [easy] lure got me hooked and I didn't want to give up on finding the final hidden message.
Looking at the cipher text, the appearance of / and + characters amongst the
alphanumeric characters made me think it was probably base64 encoded. The
cipher text ends with an = character, which reinforced my suspicions.
Decoding the starting text resulted in a binary string starting with
ÿØÿà 0x00 0x10 JFIF...
I immediately recognised this as part of a JPEG file header, so I spat the decoded text out into a file and opened it in an image editor. An alternative way of viewing the image is simply to paste the base64-encoded data into a browser's address bar like so:
data:image/jpeg;base64,/9j/4AAQSkZJRgABAQ...
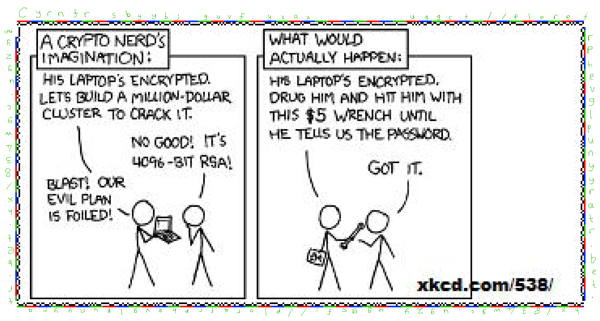
I chuckled quietly to myself as it turned out to be a smaller version of this XKCD comic:

Not the hidden code
Hmm, that seemed easy, although it didn't really seem like a 'hidden code'. Could there be more to this problem than meets the eye? The answer turned out to be yes! (much more!)
I compared the decoded image with the original one hosted at XKCD (http://imgs.xkcd.com/comics/security.png)
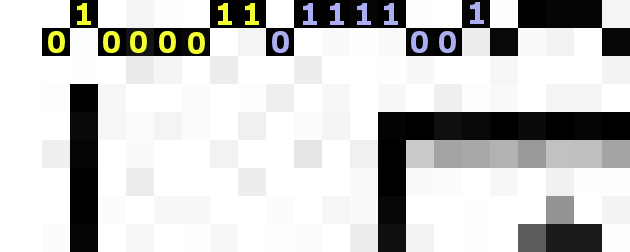
The decoded image — although slightly munged through the use of lossy JPEG compression — clearly has a frilly border drawn around it, whereas the original cartoon does not. These pixels were drawn on only one of two discrete levels around the entire cartoon, so I had a hunch that there might be a hidden message encoded in the border. I guessed that the inner pixels might represent a binary 0, while the outer pixels might represent a 1. This turned out to be a good guess:
Hiding secret information in an otherwise innocuous looking image (or text) is known as steganography, which is the art and science of writing hidden messages (from the Greek meaning "concealed writing").
Finding the next lot of ciphertext
I decoded the first two binary characters (manually) and came across "C" and "y". I must admit, I thought I was very close to the answer at that point, as I was expecting it to say "Cypher" or something similar (cypher is a chiefly British variant spelling of cipher).
However, the third character turned out to be "r", so it looked like the easy answer had gone walkies. Nonetheless, all of the characters so far were alphabetical, which might not just be a coincidence, so I continued to decode the binary around the image, which didn't take long manually. If you're particularly familiar with the binary representations of the letters a-z, then it would probably have taken longer to write a script to do this part of the task.
It was soon apparent that this was probably some kind of simple substitution cipher, as I decoded the binary into the following ciphertext:
Cyrnfr sbyybj guvf yvax: uggcf://plorefrphevglpunyyratr.bet.hx/834wgc.ugzy uggcf://plorefrphevglpunyyratr.bet.hx/834wgc.ugzy
Decrypting the ciphertext through guesswork
The first thing I noticed was the "://". It seemed reasonable to assume that these were unencoded and therefore part of a URL.
The "uggcf://" was most likely "https://", and it doesn't take a genius to realise that "plorefrphevglpunyyratr.bet.hx" is the same length as — and contains the same dots as — "cybersecuritychallenge.org.uk"
So that gives a pretty good head start on decrypting the ciphertext now that we know it's a simple symmetric substitution cipher (e.g. "a" translates to "n", "b" translates to "o", and so on).
Those guesses have already solved most of the cipher, and it becomes trivial to decipher the rest when you realise it's using a simple ROT13 translation (or perhaps the more advanced triple-rot13 encryption algorithm?).
So this decrypts to:
Please follow this link: https://cybersecuritychallenge.org.uk/834jtp.html https://cybersecuritychallenge.org.uk/834jtp.html
Third and final cipher
Rather pleased that I'd solved the cipher, I followed the link (duplicated for some reason), only to discover that it took me to a page which contained a third cipher!
https://cybersecuritychallenge.org.uk/834jtp.html displayed about 1000 characters of hexadecimal text (all on one line):
68edcdec4e2c8eae8d2c 8e2dedcd6e04d2042fed ae52ceac04ccedaecd8c 042ccd8c046cedad0e8d etc...
I was quite stumped at this point - it looked a bit harder than the previous cipher. Translating the hexadecimal digit pairs into bytes did not lead to anything intelligible, nor did it appear to be a valid image file or compressed archive.
Unable to see any obvious mapping between the hex and ordinary ASCII characters, I almost gave up. But first, I thought I'd see how frequently each hex-pair appeared in the cipher text.
Delving into space
I did notice that "04" was the most commonly used hex pair in the ciphertext, followed by "ac" with 49 occurrences. There were only 56 distinct hex pairs in use, which made me think it was probably another substitution cipher, albeit slightly more complex than the earlier rot13 one.
If this was just another substitution cipher, it seemed reasonable to assume that "04" was probably a space character.
Congratulations
Substituting in the space characters meant that the first word would have to be 15 characters long! At this stage, I guessed that this was probably the 'real' part of the challenge, and so the encrypted text was likely to be some kind of congratulations message... hang on, "Congratulations" has 15 characters!
So I substituted in the word "Congratulations" before the first space character. This lucky guess turned out to be correct, and the 12 distinct characters (11 lowercase and 1 uppercase) immediately made the rest of the partially decrypted message look plausible:
Congratulations [d2] [2f]ou[52][ce][ac] [cc]oun[8c] an[8c] [6c]o[ad][0e]l[ac]t[ac][8c] t[0d][ac] [4a][a8][28][89] [6c][0d]all[ac]ng[ac][c5] [2b]our [ee]in [6c]o[8c][ac] is [6c][2f][4c][66]r[a7]s[66][6c]ur[26]t[2f][45][6c][0d][08]ll[66]ng[ac][65][46][c6][a5] [06][e6][a5][46][06][26][06][c5] [a1][41][a1][41][0a]l[ac]as[ac] [ac][ad]ail t[0d]is [6c]o[8c][ac] to our t[ac]a[ad] at [ad][ac][8c]ia[08][6c][2f][4c][ac]rs[ac][6c]urit[2f] [6c][0d]all[ac]ng[ac][c5]org[c5]u[6d][c5] [29][cc] [2f]ou[52]r[ac] t[0d][ac] [cc]irst [0e][ac]rson to [8c]o so[85] an[8c] [6c]an [0e]ro[ce][ac] [2f]ou [ad][ac][ac]t t[0d][ac] [ac]ligi[4c]ilit[2f] [6c]rit[ac]ria [05][48]ritis[0d] [6c]iti[4f][ac]n [6c]urr[ac]ntl[2f] r[ac]si[8c][ac]nt in t[0d][ac] [aa][69][25] [ee][ac] [ee]ill [4c][ac] in tou[6c][0d] to a[8c][ce]is[ac] [0d]o[ee] to [6c]lai[ad] [2f]our [0e]ri[4f][ac][c5] [ea][ac]ll [8c]on[ac] an[8c] goo[8c] lu[6c][6d] in t[0d][ac] C[2f][4c][ac]r [6a][ac][6c]urit[2f] C[0d]all[ac]ng[ac] [6c]o[ad][0e][ac]titions ta[6d]ing [0e]la[6c][ac] t[0d]roug[0d]out t[0d][ac] r[ac]st o[cc] t[0d][ac] [2f][ac]ar[c5]
After making this initial guess, it was possible to make further educated guesses at what the other substitutions may be, such as ta[6d]ing -> taking and so on. Several other words also stand out as candidates, such as "throughout", "criteria", "security", "first person", "currently", etc. Filling in each of these words provides additional mappings, which allows other words to be gleaned. This reminded me of the approach taken by Donald and Bettye Harden when they cracked the 408-symbol cryptogram sent by the Zodiac killer in 1969.
This only got me so far, as the "win code" evidently contained some characters that were not used anywhere else in the encrypted message: there must be an algorithm for performing the mapping, rather than it being an arbitrary hand-selected set of mappings. Looking at an ordered sequence of the mappings showed that there was indeed a pattern:
'2c' => 'a', '4c' => 'b', '6c' => 'c', '8c' => 'd', 'ac' => 'e', 'cc' => 'f', 'ec' => 'g', '0d' => 'h',
See the pattern?
I guessed that the digits 1 and 3 might appear within the 'win code', in place of the letters "i" and "e" respectively (l33t style!). This seemed to fit in with the above pattern and allowed me to derive the mappings for all digits 0-9.
Decrypting the final cipher
By this point, it seemed obvious that the pattern followed the same order as the ASCII character set, which made it possible to guess the other remaining characters in the win code and complete the decryption process:
Congratulations - you've found and completed the REAL challenge. Your win code is cyb3r=s3cur1ty*ch@ll3nge+26-07-2010.
Please email this code to our team at media@cybersecuritychallenge.org.uk. If you're the first person to do so, and can prove you meet the eligibility criteria (British citizen currently resident in the UK) we will be in touch to advise how to claim your prize. Well done and good luck in the Cyber Security Challenge competitions taking place throughout the rest of the year.
Amusingly (annoyingly?), it wasn't until after I'd decrypted this that I realised how it worked: all you have to do is perform a bitwise rotate-left on each byte 3 times. However, I think the 'Zodiac' approach was more fun!
I was only trying to solve the cipher for fun, so it was a pleasant surprise to learn about there being a possible prize.
I sent my email off a couple of hours after first finding out about the cipher challenge, but subsequently discovered that the challenge had originally been announced 3 days earlier! I therefore held little hope of being the first person to have cracked the cipher, but it was a fun challenge anyway, so all was not lost.
However, to my surprise, it turned out that I was the first person to have solved it! Many others — along with myself at first — thought that they had solved it as soon as they had decoded the XKCD JPEG image, hence there being lots of tweets and blog posts about having solved it — some even stating that it wasn't much of a challenge because it was so easy. It evidently wasn't that easy if they didn't even notice the hidden ciphertext drawn around the border of the entire image :)
Final thoughts
It turned out that several people got the right answer, but most people took about twice as long as I did! The guys at PwC who developed it were "literally gobsmacked", so I guess I must have done well, and the PR chap for the Cyber Security Challenge UK said it was "a quite brilliant achievement". Allow me to revel in this praise for a moment :)
I thought it was a pretty fun challenge, which turned into something bigger than it first seemed. It appears to have been well thought out, with no ambiguities and certainly wasn't impossible (it certainly wasn't easy, either!).
I think I made a few educated guesses which helped me get towards the final solution quickly, but these perhaps would not have worked so well if more complicated ciphers had been used (even a Vigenère cipher would have required a different technique, but I'd ruled out anything as complicated as Rijndael AES and suchlike, as there would have needed to be some clues about what the IV and key might be). I'm sure my approach may have differed greatly to some other people's, but it's all down to speed in a competition like this! Automating the overall solution is nice, but for a one-off task, I felt that some parts of this challenge were better (i.e. faster), and certainly more fun, when done manually.
Maybe I'll have a look at the unsolved Zodiac ciphers next :)
Search this site
Copyright Paul Mutton 2001-2013
http://www.jibble.org/
Feedback welcomed
![]()